News & Updates
Blog
You may have seen this type of security awareness information before. But maybe this time, something will click, and you will see how things actually work. This is a game of perspective.
4 Things to Intelligently Spend Your Money On
What should you spend your extra money on after all bills and debts are paid? Let's go over the 4 things to intelligently spend your money on. 1. Invest in Yourself Buy books and audio programs. Buy online courses and learn new skills. Buy a seat to a certification...
How to Remove EXIF Data From Photos Taken With Smartphones
The Exchangeable image file format, or EXIF data, is a standard format for storing and exchanging image metadata. This information is included in an image file and provides details of the photo, including location, time, camera details, and other potentially...
How to Use OneDrive Instead of Email for Attachments
If the attachment you are trying to send to a co-worker is too large or is a file format that is commonly blocked by your email administrator, you may need to attach your file using OneDrive. 1. Sign in to the Office Portal with your email address and computer...
Most Common Passwords of 2018
Once again, in the most common passwords of 2018, SplashData returns with the 2018 Worst Passwords of the Year list. This list was determined after evaluating over 5 million passwords that have leaked online in the last year. Most Common Passwords of 2018 by...
How to Check Blocked and Safe Senders List if Filtering Is Bypassed
If you don't get the email you were expecting and find that filtering was skipped, this article will show you what to do next. First, you or your email admin have determined that an email message is blocked after looking at the tags. Here's the full notification:...
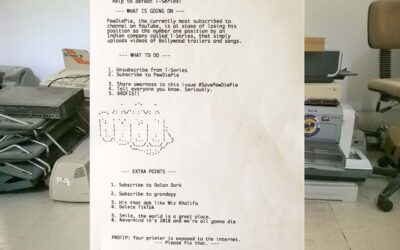
About That Subscribe to PewDiePie Printer Hack
Another interesting hack in the works shows printers are computers, too. This has to do with that "PewDiePie printer hack." https://twitter.com/apex2504/status/1067512945322676230 People are posting printer hacks of weird messages to Twitter. This is regarding a...
Identity Theft Prevention Essentials
Identity theft prevention is one of the most important things you can do. Identity theft is when criminals use personal information such as social security numbers, banking or financial account numbers, and passwords to steal money or obtain credit illegally. It can...
How To Create More Secure Security Questions
When you set up a new online account, the website or service will usually ask you to select security questions and then answer them. This is to verify your identity as a second layer of login protection. Some websites enforce a security answer upon every login, and...
Most Common Passwords of 2017
SplashData has published its annual list of the worst passwords of the year using data from more than 5 million passwords that were leaked by hackers. SplashData also commented on the number of well known breaches that have occurred within the last year (or 2)....
LT’s Personal Finance Commandments
This post has a list of personal finance commandments from a professor I admired. What made him so great was his drive to make you succeed outside of the classroom. My favorite bits of the class were when we talked about applicable money making topics instead of the...
Reminder, Printers are Computers Too
That's right. Printers are computers, too. Remember when we found out a Canon Pixma printer could run Doom? That fun hack was nearly 3 years ago (at least published 3 years ago, anyway). A security researcher from Context Information Security used modified firmware...
Most Common Passwords of 2016
It's time for SplashData to release its annual list of the most common passwords of 2016, but first, let's start with a password list from Keeper Security. Most Common Passwords of 2016 by Keeper Security The company analyzed over 10 million passwords publicly...